Twenty-nine minutes.
That’s the average time it takes a cybercriminal to move from an initial compromise to lateral movement across a network, according to CrowdStrike’s 2026 Global Threat Report. The fastest recorded breakout last year took 27 seconds. In one case, data exfiltration began within four minutes of initial access.
The window for detection and response has never been smaller, and it continues to shrink. The same report found that AI-enabled attack operations surged 89% year over year in 2025, while 82% of detections involved no malware at all. Attackers are logging in with stolen credentials, abusing trusted tools, and blending into normal network activity. Traditional signature-based defenses can’t keep pace with adversaries who don’t look like adversaries.
Security teams need a framework built around attacker behavior rather than static indicators. The MITRE ATT&CK framework provides exactly that. Putting it to work starts with understanding what today’s attackers are actually doing once they’re inside your environment.
What is ATT&CK?
ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. Created by MITRE in 2013, the framework is a free, globally accessible knowledge base that documents how real-world attackers operate. It catalogs specific tactics (the why behind an action), techniques (the how), and procedures (the step-by-step execution) that threat actors use across every stage of an intrusion.
The Enterprise matrix alone, as of the October 2025 v18 release, contains 14 tactics, 216 techniques, and 475 sub-techniques. MITRE also maintains separate matrices for Mobile and Industrial Control Systems (ICS), reflecting how attack surfaces have expanded into mobile devices, IoT, and embedded systems.
Think of ATT&CK as the attacker’s playbook, but in the defender’s hands. Adversaries chain together multiple behaviors across different phases of an intrusion. Each phase consists of a tactic supported by a set of techniques, carried out through specific procedures. That layering is where the acronym TTP comes from: tactics, techniques, and procedures.
The v18 release also overhauled the framework’s defensive side, replacing traditional detection entries with Detection Strategies and Analytics. This version provides more actionable, structured guidance on how to catch attacker behaviors in real environments, not just catalog them.
What is the pyramid of pain?
Not all threat indicators carry equal weight. David Bianco’s Pyramid of Pain captures this well.
At its base sit hash values and IP addresses. Easy to detect, but just as easy for attackers to rotate. Move higher through domain names, network artifacts, and tools, and you start making the attacker’s job harder. They have to retool, rebuild infrastructure, and invest more time.
At the apex are TTPs. When your defenses detect and respond to behavior rather than static indicators, the attacker’s entire playbook breaks down. They can’t just swap a file hash or rotate a domain. They must rethink their entire approach, and most threat actors, outside of well-funded nation-state groups, either can’t or won’t do that.
ATT&CK gives security teams a structured way to build detections at the top of that pyramid, where they do the most damage to an adversary’s operations.
Four ways security teams put ATT&CK to work
ATT&CK provides a common vocabulary for sharing threat information and building detection and response procedures. Security teams typically apply it in four ways:
- Threat intelligence: Map the tactics and techniques adversaries actively use against your industry to anticipate threats before they arrive.
- Detection and analytics: Build detection rules around specific ATT&CK techniques. The v18 framework now includes structured Detection Strategies and Analytics to support this directly.
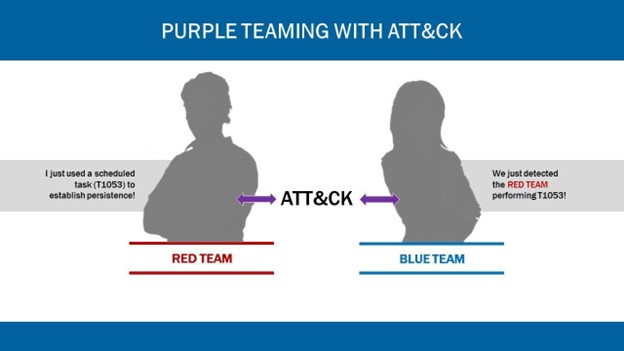
- Adversary emulation and purple teaming: Replicate real attacker TTPs and test whether your defenses catch them. Red teams chain techniques across tactics to probe for weaknesses; blue teams use the same framework to validate their response.
- Assessment and engineering: Evaluate how current defenses stack up against ATT&CK techniques, identify coverage gaps, and prioritize investments.
 Where to start when the framework feels overwhelming
Where to start when the framework feels overwhelming
Hundreds of techniques, thousands of analytics, dozens of threat groups. The instinct is to try to cover everything. Resist it. The organizations that get the most from ATT&CK start with their own environment and work outward.
- Know yourself. Identify your most valuable assets, where sensitive data resides, how it flows, and where attackers would focus. That turns hundreds of techniques into a manageable set of priorities.
- Avoid analysis paralysis. Focus on the techniques most relevant to your industry, infrastructure, and likely threat actors. A financial services firm and a healthcare system face overlapping but distinct profiles, and their ATT&CK priorities should reflect that.
- Consider levels of difficulty. Some techniques require more sophisticated tooling or expertise to detect. Align your list with your team’s current capabilities. Build wins early, then expand.
- Confirm your data sources. A detection is only as good as the telemetry behind it. Start with the data sources you already have, maximize the detections you can build from those, and use the gaps to guide future investments.
- Evaluate solutions that help you automate. Many leading security vendors integrate with ATT&CK, enabling SOC teams to incorporate threat intelligence directly into their workflows. Define your use cases and preferred capabilities before choosing tools.
This is not a one-time fix
One of the most common mistakes with ATT&CK is treating it as a project rather than a process. You map your environment, build some detections, and check the box. But the threat landscape doesn’t sit still, and neither does the framework.
Patching alone remains one of the most persistent challenges across organizations of every size. Modern environments span on-premises infrastructure, cloud workloads, SaaS applications, and third-party integrations, and no team can address every vulnerability simultaneously. ATT&CK helps focus that effort, identifying where controls will have the greatest impact based on the behaviors attackers are most likely to use.
Security is always a balancing act between protection, cost, and business continuity. ATT&CK provides a structured way to make smarter decisions within that tension, but only if you treat it as a living practice rather than a one-and-done exercise.
Turning framework guidance into real-world defenses
ATT&CK tells you what good security practices look like. It doesn’t tell you which solutions to deploy, how to configure them, or whether your current setup aligns with the controls it recommends. That’s where SHI comes in.
Our cybersecurity practice helps organizations connect ATT&CK’s guidance to the technology, people, and processes required to act on it.
Whether you need identity and access management, application security, data-centric protection, cloud and network security, threat and vulnerability management, or program strategy and operations, our experts can assess the current state, recommend solutions, and validate that implementations work as intended.
Some come with a specific gap to close; others want a comprehensive assessment against ATT&CK, NIST 800-53, or industry-specific requirements like HIPAA, PCI, or SEC guidelines. Either way, we work across the full lifecycle, including advisory, solution design, implementation, and testing.
Cybersecurity is a three-legged stool: technology, people, and process. ATT&CK gives you the blueprint. SHI helps you build the stool.
The attackers are faster. Your response must be as well
The average breakout time has collapsed from hours to minutes. Most intrusions occur without a single identifiable piece of malware. ATT&CK won’t solve all of that on its own, but it gives security teams a structured, behavior-based approach to building defenses that match today’s threat actors’ speed and sophistication.
The attackers aren’t going to slow down. Your defenses shouldn’t either.
NEXT STEPS
Want to know where your security gaps are? Connect with our cybersecurity team to assess your environment against the ATT&CK framework and build a plan to close them.
PakarPBN
A Private Blog Network (PBN) is a collection of websites that are controlled by a single individual or organization and used primarily to build backlinks to a “money site” in order to influence its ranking in search engines such as Google. The core idea behind a PBN is based on the importance of backlinks in Google’s ranking algorithm. Since Google views backlinks as signals of authority and trust, some website owners attempt to artificially create these signals through a controlled network of sites.
In a typical PBN setup, the owner acquires expired or aged domains that already have existing authority, backlinks, and history. These domains are rebuilt with new content and hosted separately, often using different IP addresses, hosting providers, themes, and ownership details to make them appear unrelated. Within the content published on these sites, links are strategically placed that point to the main website the owner wants to rank higher. By doing this, the owner attempts to pass link equity (also known as “link juice”) from the PBN sites to the target website.
The purpose of a PBN is to give the impression that the target website is naturally earning links from multiple independent sources. If done effectively, this can temporarily improve keyword rankings, increase organic visibility, and drive more traffic from search results.



