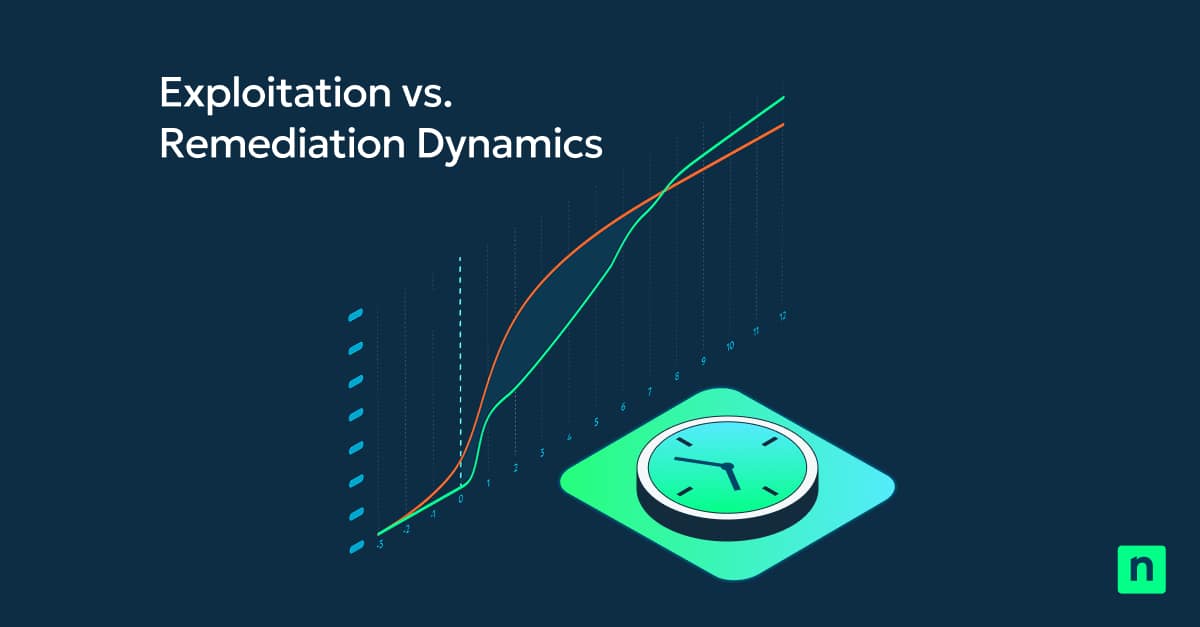
By the time a patch is released, a vulnerability is likely already being actively exploited. The vulnerability is originally introduced in code and the exploit may already be days, weeks, or even months old. More than half of vulnerabilities are exploited within the first 48 hours and the average time to patch more than 200 days. This, operational exposure gap leaves organizations at risk far too long.
Response times are often slowed by scheduled scan windows, manual handoffs between SecOps and IT Ops, and disconnected workflows. The time between vulnerability disclosure and effective remediation creates the operational exposure gap.
Why scan-driven vulnerability management falls short
Scan-driven vulnerability management wasn’t built for today’s dynamic threat landscape. It relies on periodic, resource-intensive scans that deliver point-in-time results in a real-time threat environment. As the sheer volume of CVEs increases year after year, traditional models cannot keep pace.
Scan-based vulnerability detection creates predictable friction:
- Delayed visibility
- Outdated report data
- Extended exposure windows
- Slow or complex handoffs between Security and IT
Vulnerability management must evolve. Detection and remediation should be more tightly connected, so vulnerabilities can be addressed immediately instead of waiting for the next scan cycle.
NinjaOne is changing the game
NinjaOne Vulnerability Management with Real-Time Assessment shifts vulnerability detection from a periodic, scheduled event to a continuous, risk-aware process. We didn’t create a “better” scanner. In fact, NinjaOne removes scanning from the vulnerability management process entirely. AI correlates live endpoint software telemetry with current CVE intelligence without scheduled scans, agent spikes, or endpoint performance impact.
NinjaOne Real-Time Assessment can identify up to 90 percent of software-related CVEs within minutes of a software installation or configuration change. AI-powered models map software metadata directly to CVE definitions, delivering nearly instant vulnerability awareness. Your SecOps and IT Ops teams no longer need to manage scan schedules, wait for results, or worry about device slowdowns. This continuous visibility remains aligned to the current state of every endpoint.
We’ve removed scanning from the critical path to remediation allowing vulnerability risk to trigger remediation. This reduces exposure windows from days or weeks to just minutes. The result is faster remediation through vulnerability management that is continuous, risk-aware, execution-focused, and operationally owned by IT.
AI-powered vulnerability management and autonomous remediation
AI plays a critical role in three areas of vulnerability management:
- Software identification across inconsistent endpoint data
- Normalization of software naming and versions
- Real-time correlation of software to CVE intelligence
NinjaOne Vulnerability Management integrates directly with NinjaOne Autonomous Patch Management, enabling vulnerabilities to be remediated immediately, within the same platform without separate tools, exports, or handoffs. This transforms vulnerability management from a siloed security function into a continuous, automated IT workflow that delivers:
- Always-on vulnerability visibility
- Accelerated automated remediation
- Reduced exposure windows
- Continuous remediation tracking
Vulnerability Management is designed to accelerate IT access to vulnerability data. Remediating vulnerabilities relies on NinjaOne Autonomous Patch Management, enhanced with Patch Intelligence AI, which analyzes vendor signals, community telemetry, and real-world deployment outcomes to determine patch safety and risk. Risky OS patches are paused. Safe patches proceed based on defined policies. The result is faster remediation, less operational disruption, and lower risk without destabilizing endpoints.
The future of vulnerability management
The future of vulnerability is continuous, real-time, and execution-driven. It’s critical to acknowledge that by the time you scan, you’re already behind. Also, that detection doesn’t reduce risk, remediation does. Organizations that eliminate scan delays and connect detection directly to remediation will dramatically reduce exposure shifting the advantage away from attackers.
Learn more: ninjaone.com/vulnerability-management
PakarPBN
A Private Blog Network (PBN) is a collection of websites that are controlled by a single individual or organization and used primarily to build backlinks to a “money site” in order to influence its ranking in search engines such as Google. The core idea behind a PBN is based on the importance of backlinks in Google’s ranking algorithm. Since Google views backlinks as signals of authority and trust, some website owners attempt to artificially create these signals through a controlled network of sites.
In a typical PBN setup, the owner acquires expired or aged domains that already have existing authority, backlinks, and history. These domains are rebuilt with new content and hosted separately, often using different IP addresses, hosting providers, themes, and ownership details to make them appear unrelated. Within the content published on these sites, links are strategically placed that point to the main website the owner wants to rank higher. By doing this, the owner attempts to pass link equity (also known as “link juice”) from the PBN sites to the target website.
The purpose of a PBN is to give the impression that the target website is naturally earning links from multiple independent sources. If done effectively, this can temporarily improve keyword rankings, increase organic visibility, and drive more traffic from search results.